Learn how to configure Microsoft Defender for Endpoint for your Windows 365 cloud PCs and physical endpoints via Microsoft Endpoint Manager
Security is one of the most important elements of choosing a virtual desktop solution for most businesses. Moving your VDI solution to a DaaS solution in the Cloud brings mostly the same value from a remoting – data consolidation perspective.
“True security is preparing for what’s next!”
However, what’s happens inside your Cloud PCs is even more important to keep viruses and other badness—in a proactive manner—out of the door. This is where Microsoft Defender for Endpoint can fulfill that extra level of security for your Cloud Managed Endpoint.
Microsoft Defender for Endpoint is Microsoft’s enterprise endpoint security platform which is created to help businesses to prevent, investigate, detect, and respond to threats. This serves to increases the level of security of your whole endpoint configuration. This applies to both virtual desktops running on the Cloud or on your physical Windows 10 Endpoints.
Learn in this article how you can configure Microsoft Defender for Endpoints via Microsoft Endpoint Manager for your Windows 365 cloud PCs and physically managed endpoints.
Read more about Windows 365 here Get started with Windows 365 – Microsoft Tech Community
Table of Contents
Click on the title to jump to that spot in this article:
- What is Microsoft Defender for Endpoint
- Why secure passwords and MFA are important too!
- Are you using Symantec or McAfee? Learn here how to switch.
- Requirements for Defender for Endpoint
- Learn how to configure Defender for Endpoint
- Alerts and Security assessments
- Security recommendations
- New MS Learn modules on Defender for Endpoint
- Need help? Visit the Defender Tech Community page
What is Microsoft Defender for Endpoint
In a nutshell, Microsoft Defender for Endpoint shares the same unified management experience benefits as Microsoft Endpoint Manager – as it’s also a holistic, cloud-delivered service. Microsoft Defender for Endpoint is a security solution that includes risk-based vulnerability management and assessment, attack surface reduction, behavioral-based and cloud-powered next-generation protection, endpoint detection and response (EDR), automatic investigation and remediation, managed hunting services, rich APIs, and unified security management.
More info: Microsoft Defender for Endpoint, Microsoft 365
Integration with Microsoft Endpoint Manager
Microsoft Endpoint Manager (MEM) becomes more and more prominent for customers that are using Azure Virtual Desktop as it provides a unified way of configuring and maintaining your physical and virtual Cloud endpoint as well as other devices e.g. mobiles.
Microsoft Defender for Endpoint integrates seamlessly into Microsoft Endpoint Manager. You only must activate the Intune integration ones during the initial setup and your reports will flow into MEM. The steps to do this are all covered later in the article.
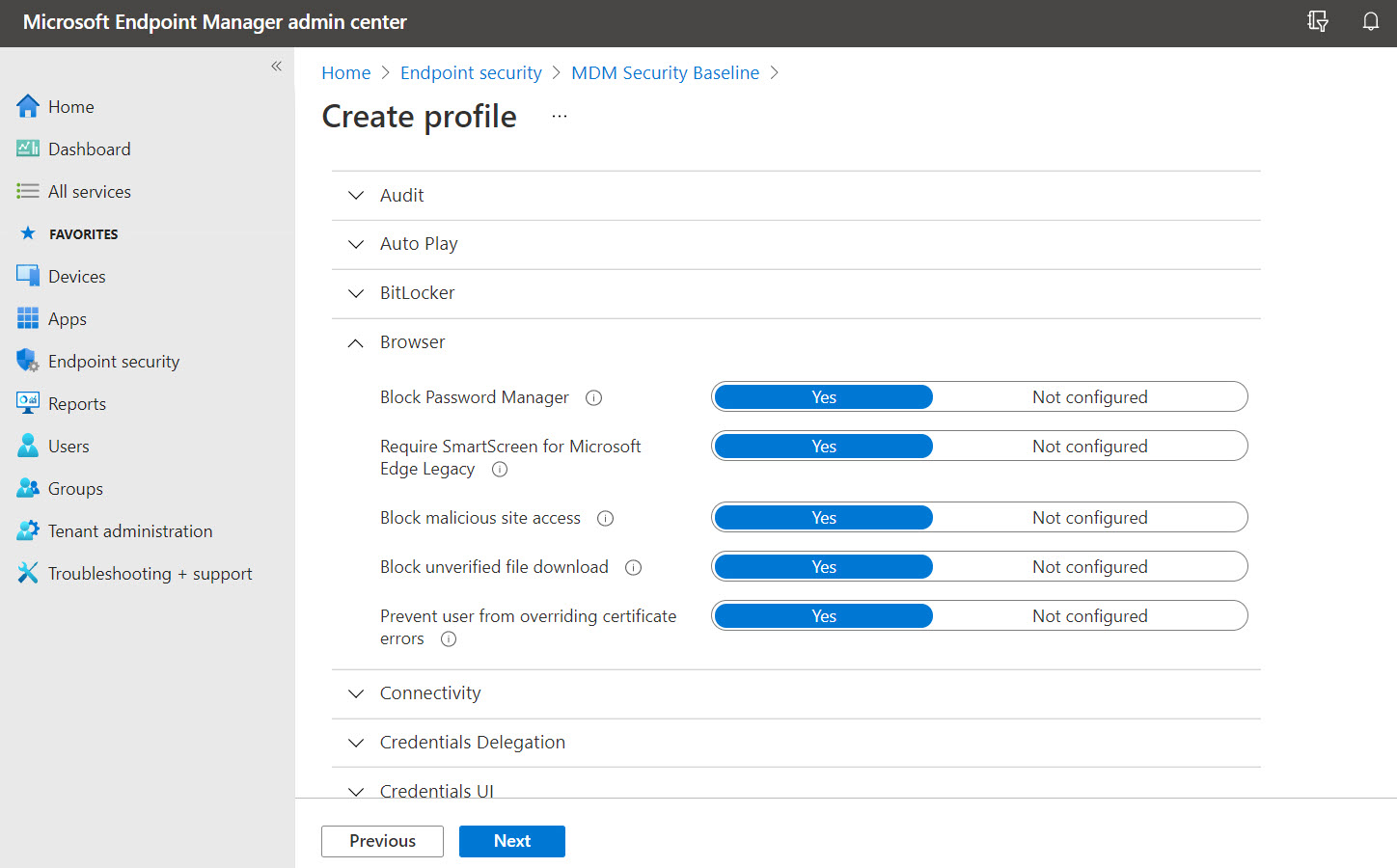
Security baselines
Security baselines are pre-configured groups of Windows settings that help you apply the security settings that are recommended by the relevant security teams. You can also customize the baselines you deploy to enforce only those settings and values you require.
There are multiple security-related settings in Windows as well as for Microsoft Edge for your endpoints. Another great asset is the option to do versioning and filtering based on different Operating Systems or scenarios that have to be more strict. You no longer have to use GPOs to ensure that the security settings on your endpoints – just create a Security baseline profile and you’re all set.
Compliance policy
Define the rules and settings that users and devices must meet to be compliant. Include actions that apply to devices that are non-compliant. Actions for non-compliance can alert users to the conditions of noncompliance and safeguard data on non-compliant devices.
See below an example of how you can set the risk level within Microsoft Defender when your endpoint does not meet the compliance expectations. Your device will show up as risk in Windows Defender for Endpoint as well as in Intune – marked as uncompliant.

Why secure passwords and MFA are important too!
I’ve written more articles about the importance of using Azure Multi-Factor Authentication and how you can activate this. This keeps most intruders out – and proactively avoids that other people can get access to your DaaS environment with only the password.
“Passwords are like underwear: don’t let people see it, change it very often, and you shouldn’t share it with strangers.”
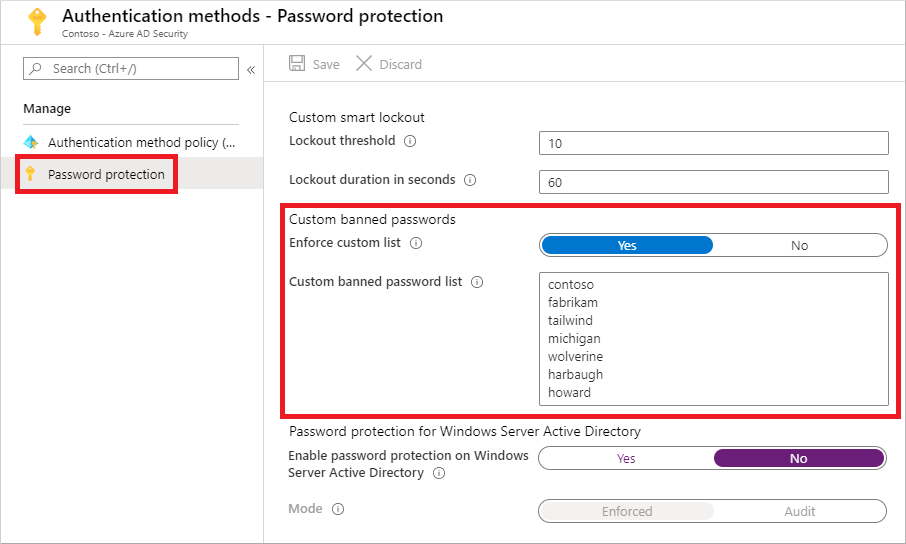
Avoid bad passwords with the Azure AD password protection feature. With the Azure AD Password Protection, default global banned password lists are automatically applied to all users in an Azure AD tenant. To support your own business and security needs, you can define entries in a custom banned password list.
Read more on Microsoft Docs here: Password protection in Azure Active Directory | Microsoft Docs
Are you using Symantec or McAfee? Learn here how to switch
The vast majority (Source: VDILIKEAPRO survey 2020) of traditional virtual desktop deployments, whether that’s RDS, Citrix or VMware are using either Symantec (Broadcom now) or McAfee Security Suite for VDI next to the built-in Defender capabilities or Windows). The process of moving to Microsoft Defender for Endpoint is relatively easy to perform and completely documented on Microsoft Docs. You can find it via the links below.
- Migration process for Symantec: Migrate from Symantec to Microsoft Defender for Endpoint – Windows security | Microsoft Docs
- Migration process for McAfee: Migrate from McAfee to Microsoft Defender for Endpoint – Windows security | Microsoft Docs
Requirements for Defender for Endpoint
Learn here about the required licenses that are needed in order to use the features mentioned in this blog article. Read more about it here Minimum requirements for Microsoft Defender for Endpoint – Windows security | Microsoft Docs
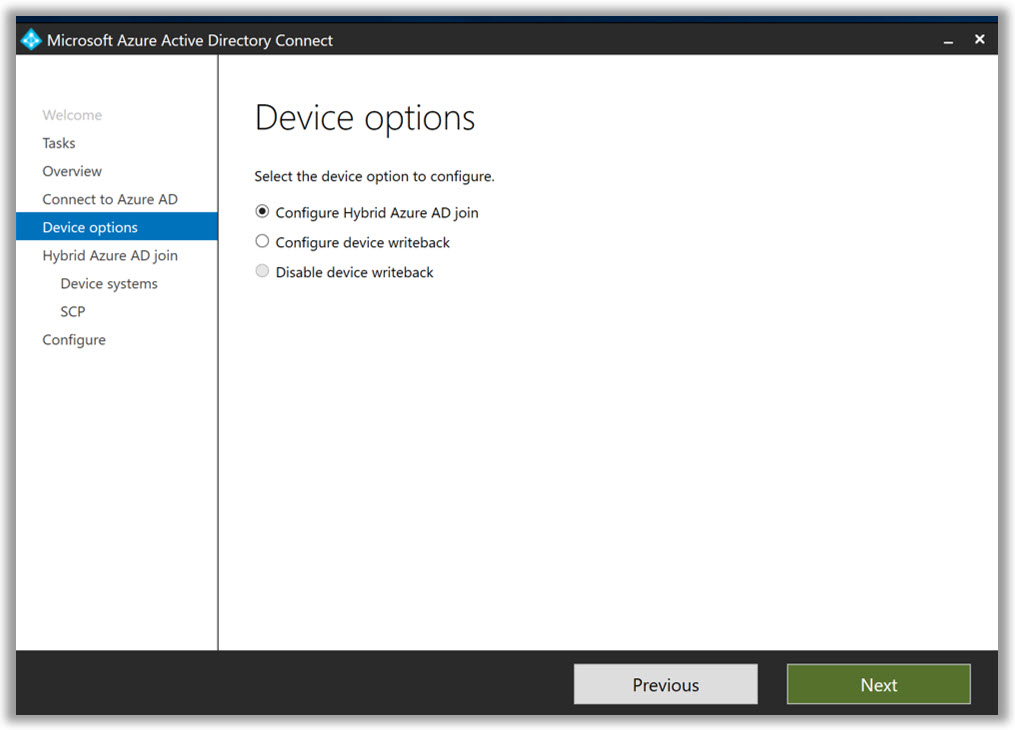
Make sure that your endpoints are Intune managed
Before we start, make sure that your environment is Hybrid Azure Active Directory enabled – or Azure AD only – and that your desktops are enrolled and possible to manage via Microsoft Intune via Microsoft Endpoint Manager.
Learn how to configure Defender for Endpoint
In the next part of this article, I’m going to explain how you configure Microsoft Defender for Endpoint via Microsoft Endpoint Manager to secure your virtual or physical Windows endpoints.
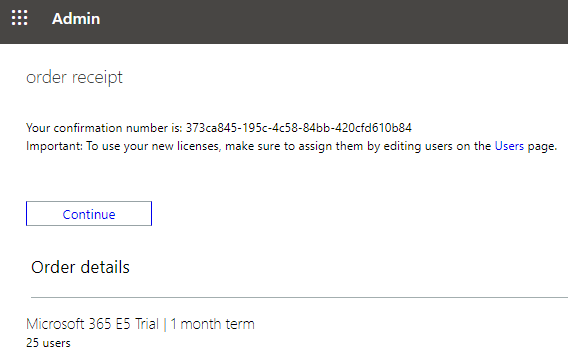
Request the right license
You can use a trial license to try Microsoft Defender for Endpoint, too.
Activate Microsoft Defender Security Center
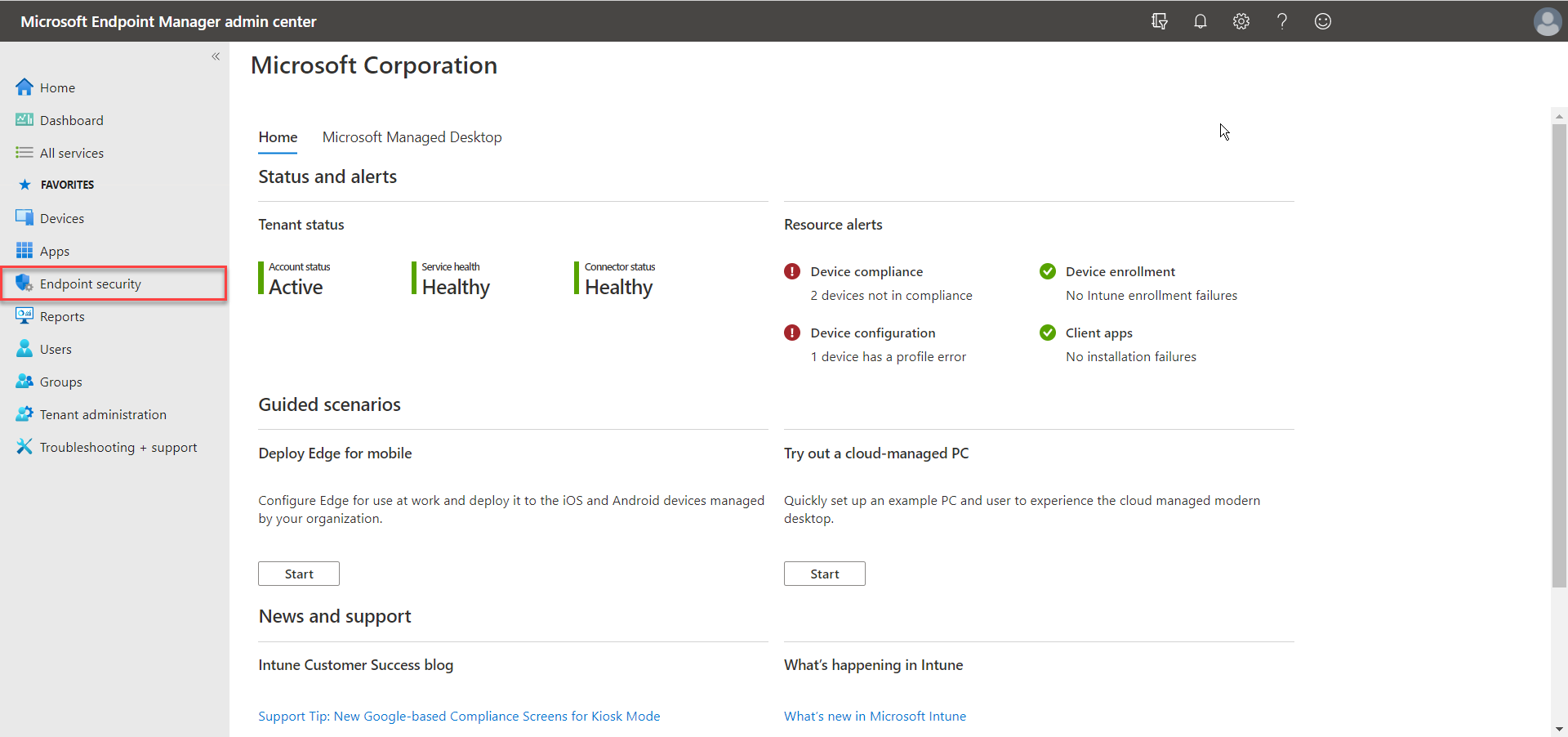
Go to the Microsoft Endpoint Manager admin center
Go to Endpoint security
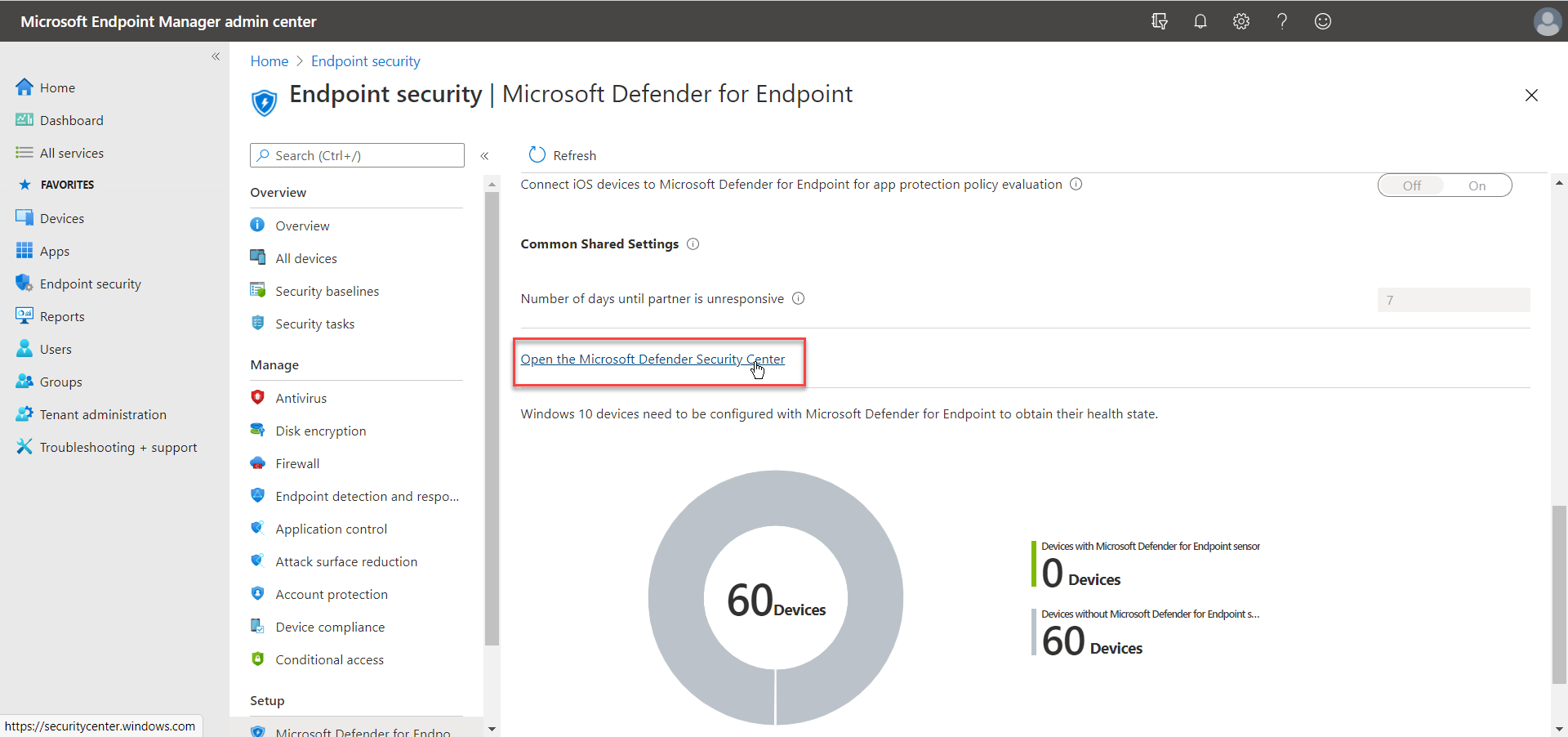
Click on – Open the Microsoft Defender Security Center
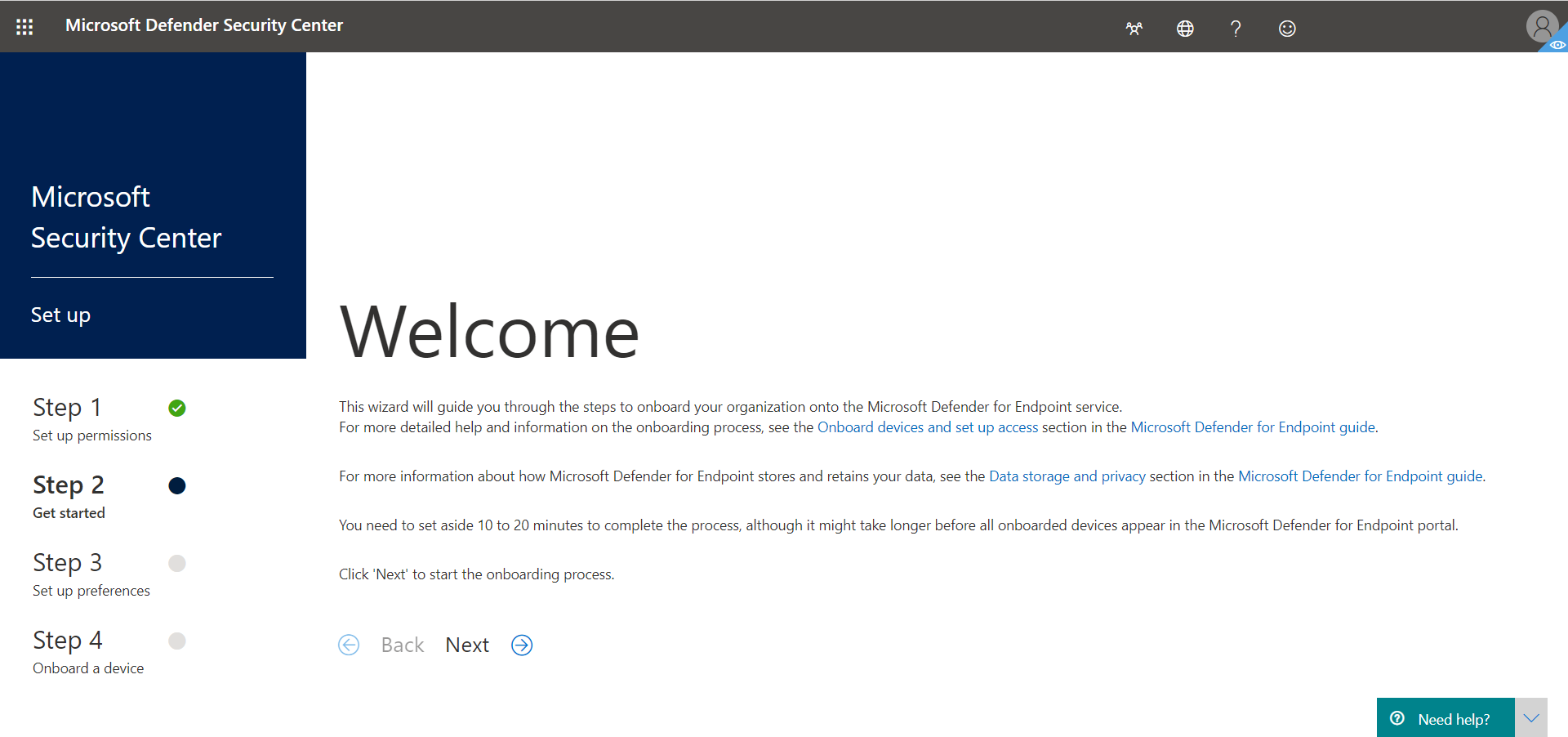
Click on Next
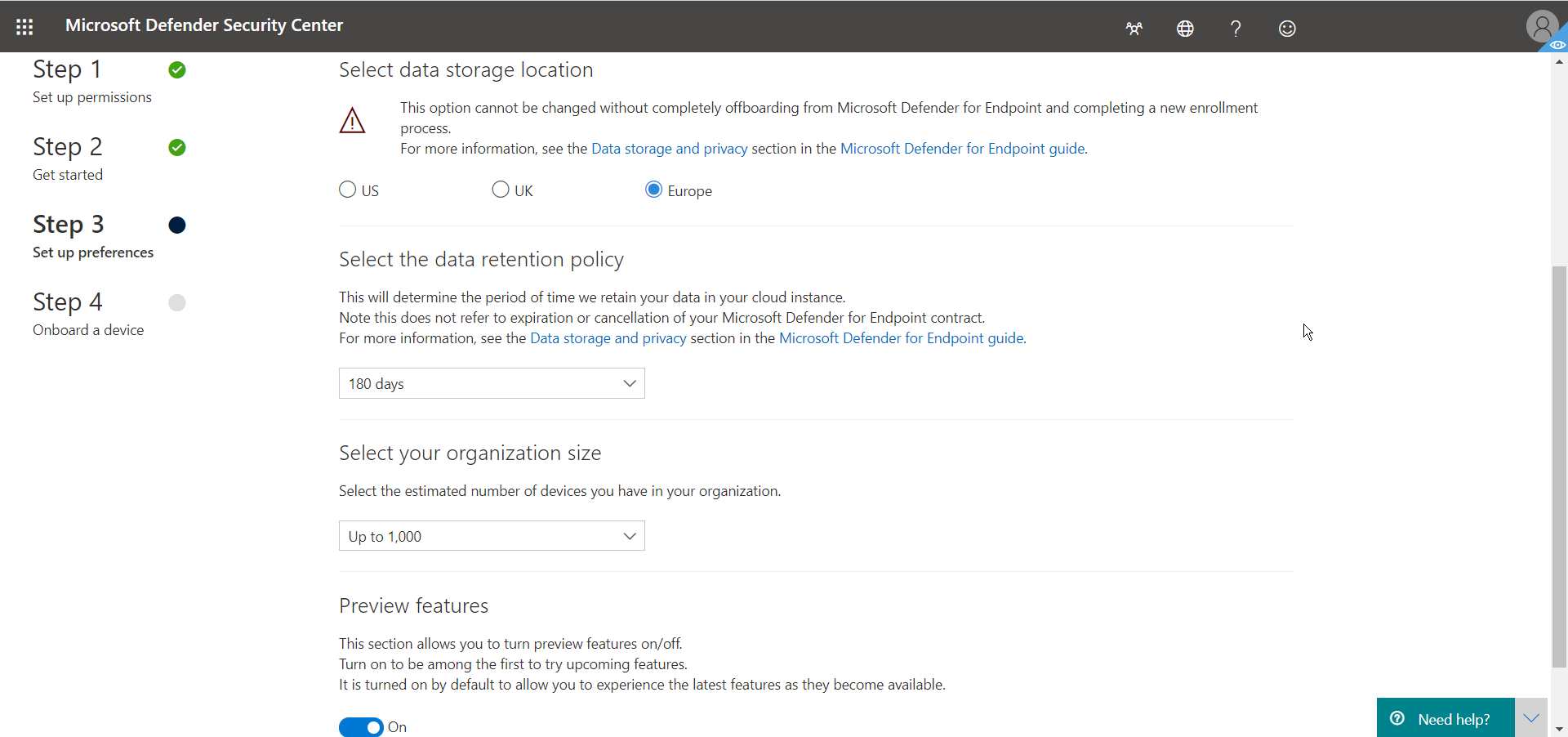
Give in your region, data retention policy time and org size.
Note: You could also try the Preview features option to be among the first to try upcoming features.
Click Next
Make sure all the settings are correct, as there is no way back.
Click on Continue
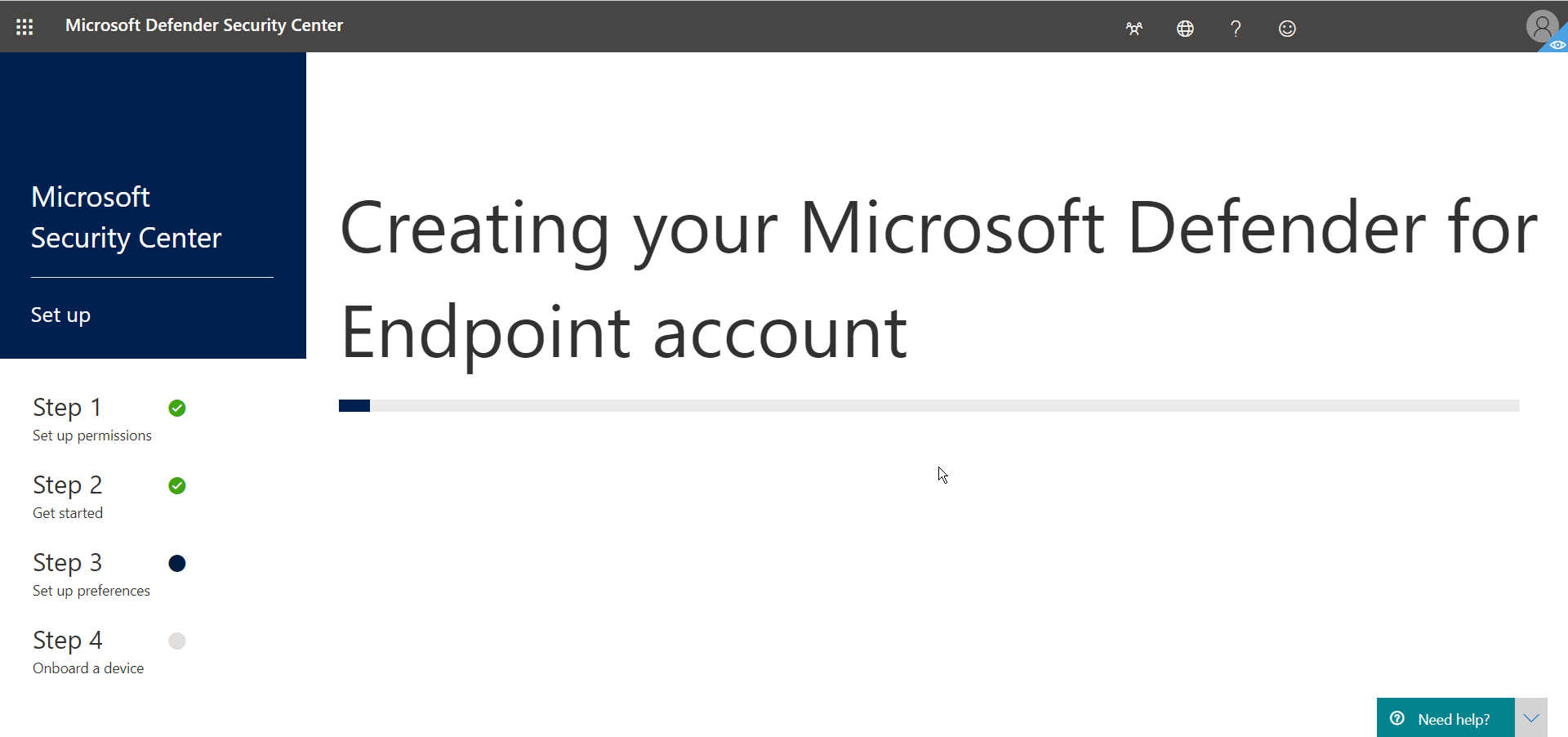
Your Microsoft Defender for Endpoint Account is being created… Please wait.
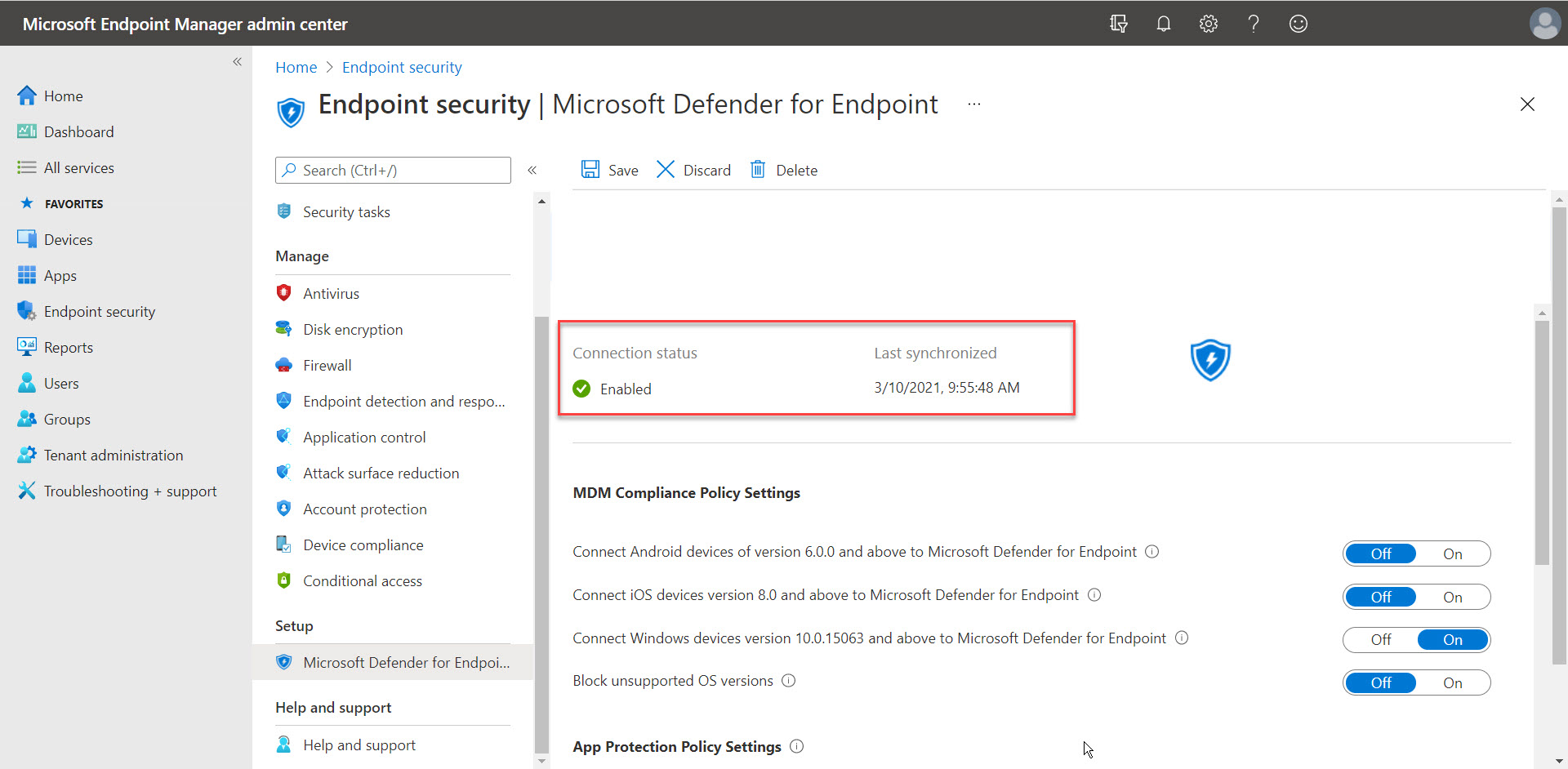
Connect to Intune – Microsoft Endpoint Manager integration
Open the Security Center portal
Go to Settings

Turn the slide to On – next to Microsoft Intune Connection
Click on save preferences
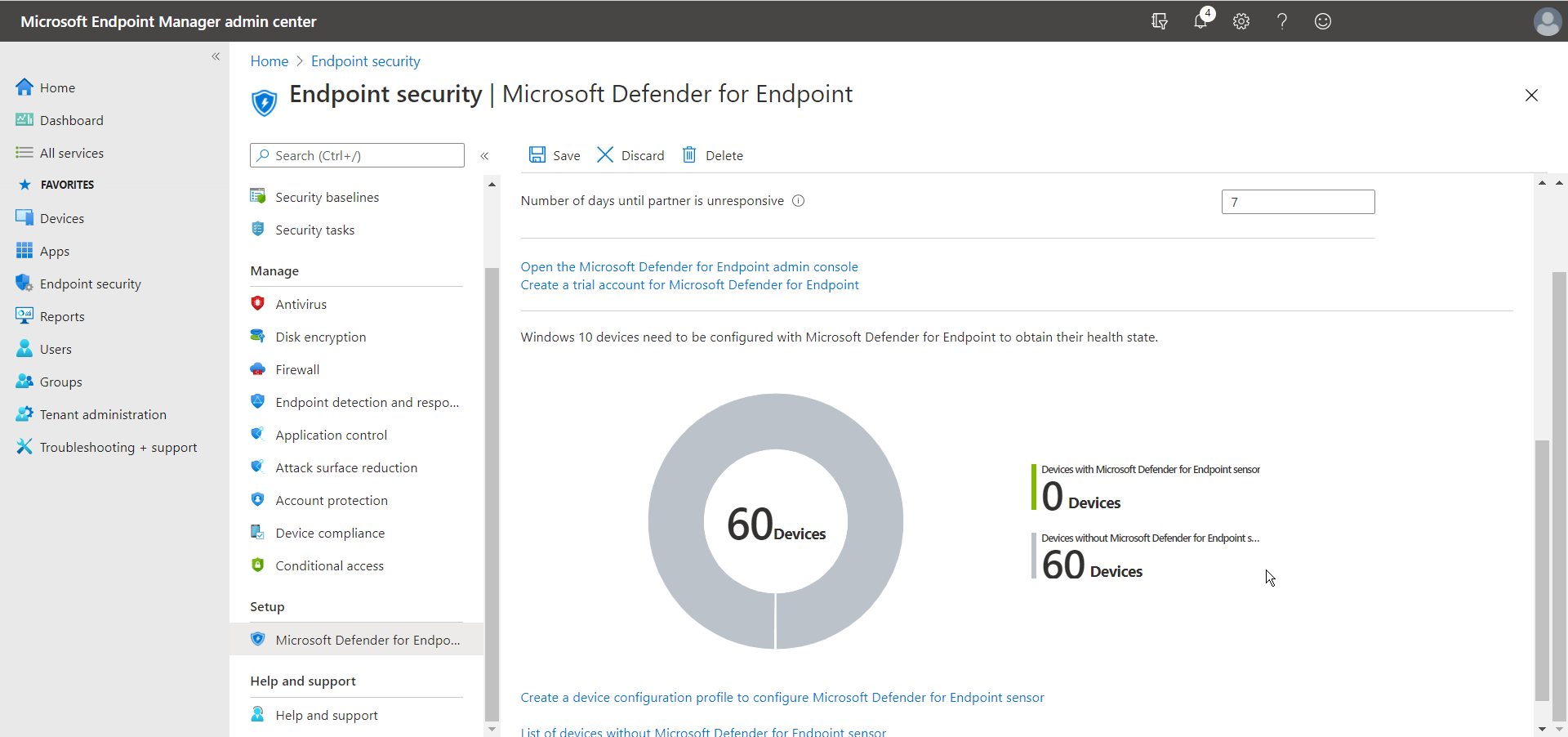
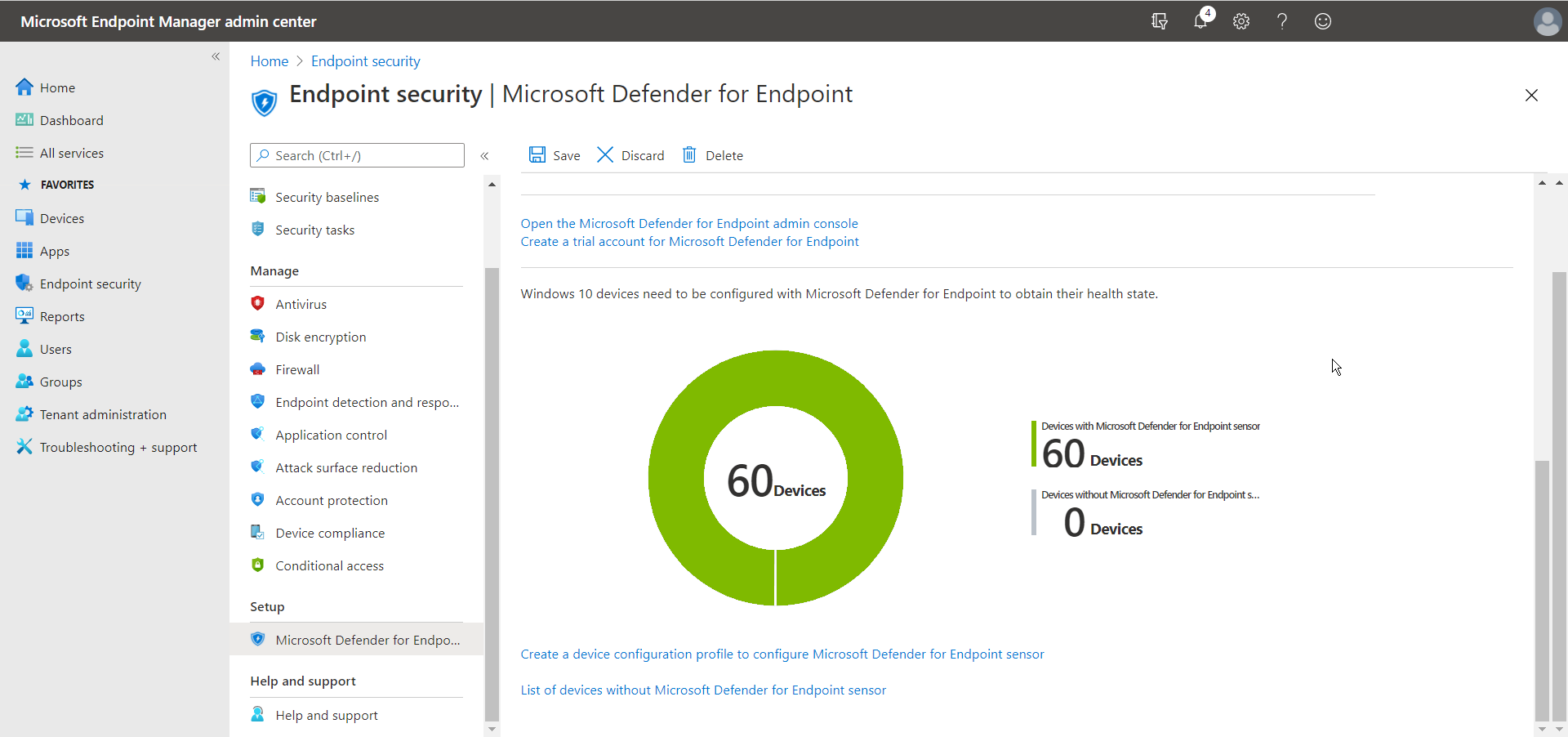
At this point, Microsoft Defender integrates into Microsoft Endpoint Manager. You can check the status in the Endpoint security menu.
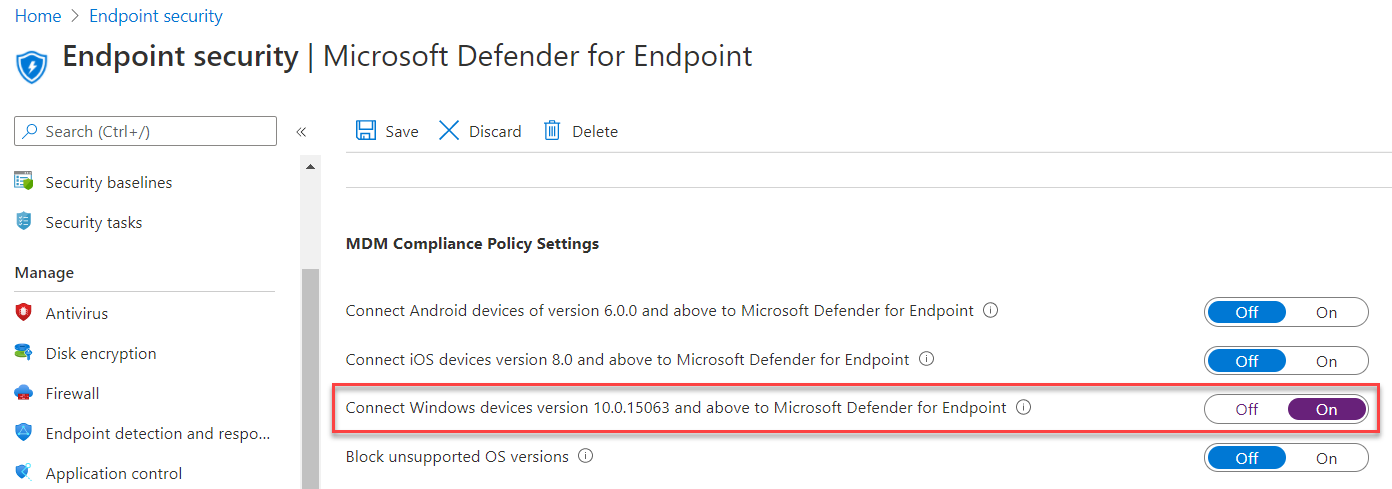
Also, make sure to enable the setting Connect Windows devices version 10.0.15063 and above to Microsoft Defender for Endpoint
Note: When on, compliance policies using the Device Threat Level rule will evaluate devices including data from this connector. When off, Intune will not use device risk details sent over this connector during device compliance calculation for policies with a Device Threat Level configured. Existing devices that are not compliant due to risk levels obtained from this connector will also become compliant.
We now need to enroll our Windows endpoints into Defender.
Onboard your Windows Endpoints into Microsoft Defender via MEM
Switch back to the Microsoft Endpoint Manager Portal
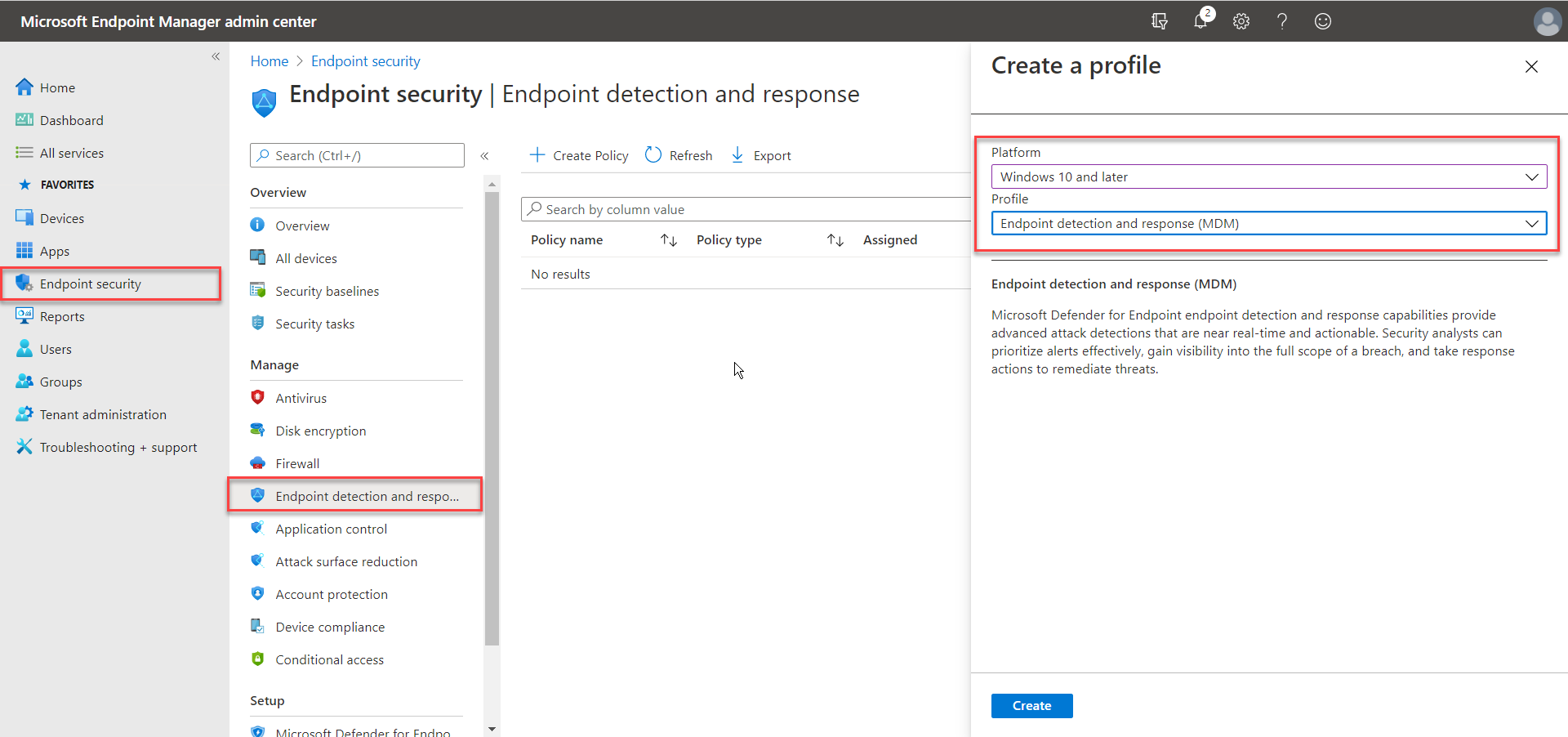
Go to Endpoint security followed by Endpoint detection and reporting
Select Windows 10 and later and Endpoint detection and response (MDM)
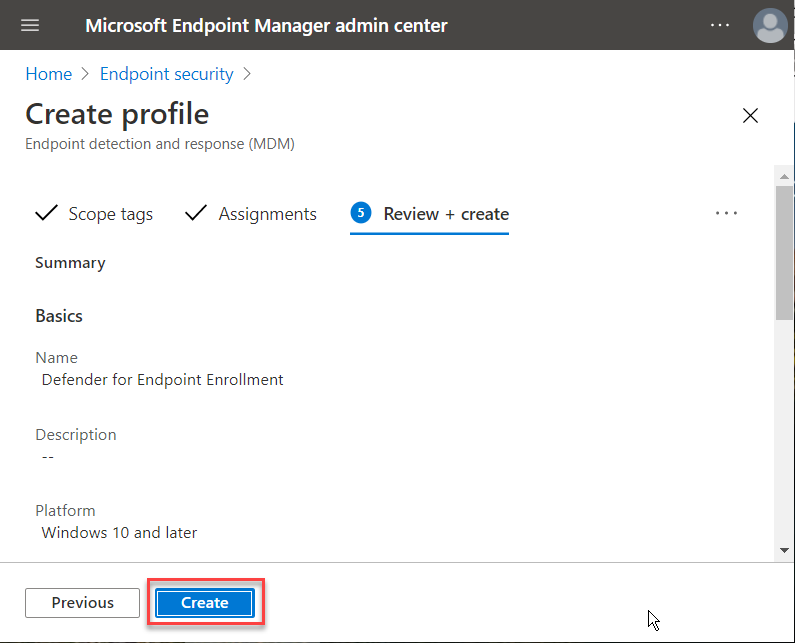
Enter in a Name
Click Next
Enable the Expedite telemetry setting.
Click on Next
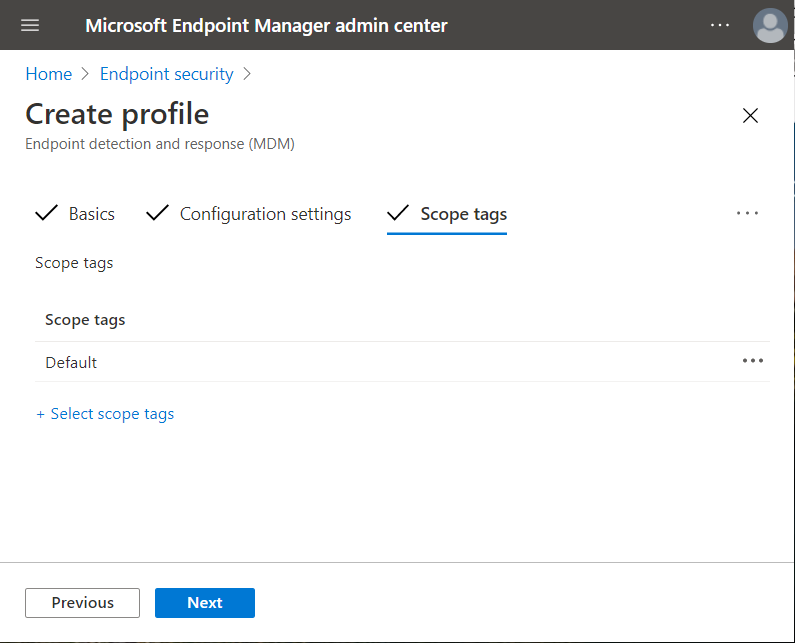
Click next
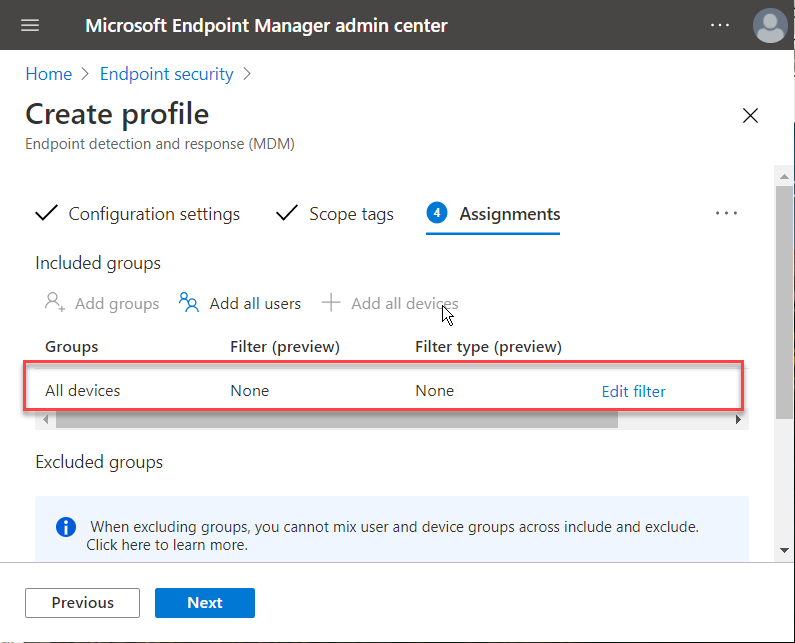
Click on + Add all devices
Click next
Click on Create
Confirm that the rule is saying Yes, under assigned.
Verify the Windows Endpoint into Defender onboarding
You should now see the status of your Windows 10 virtual or physical endpoint changing from without to devices with Microsoft Defender for Endpoint enabled!
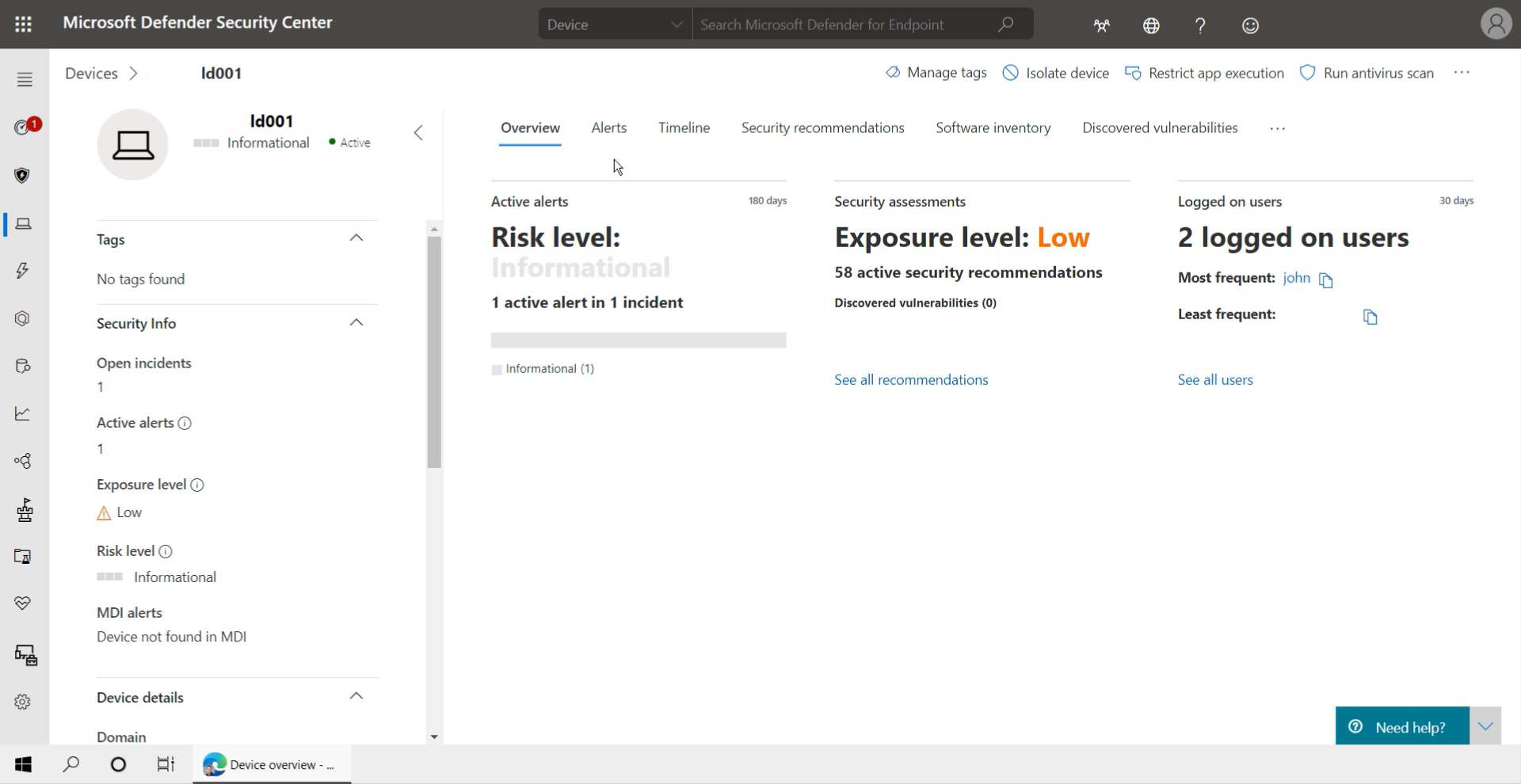
Alerts and Security assessments
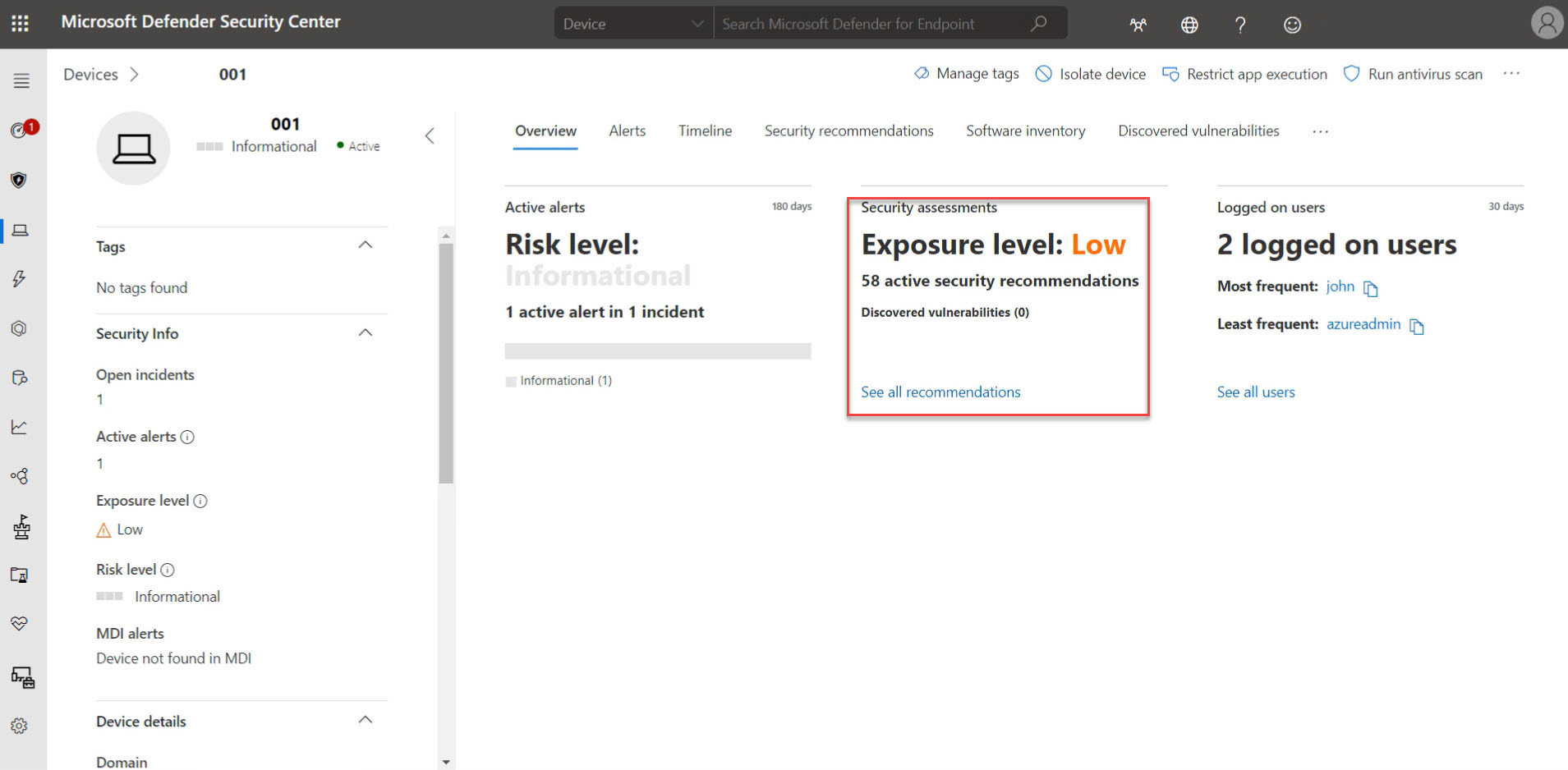
Once the rollout and activation are done, configured some security baselines and compliance profiles and assigned them to your desktops – you are ready to review your devices in the Microsoft Defender Security Center console. When you click on devices, you’re able to drill down into the different assessments and alerts (if any) being detected.
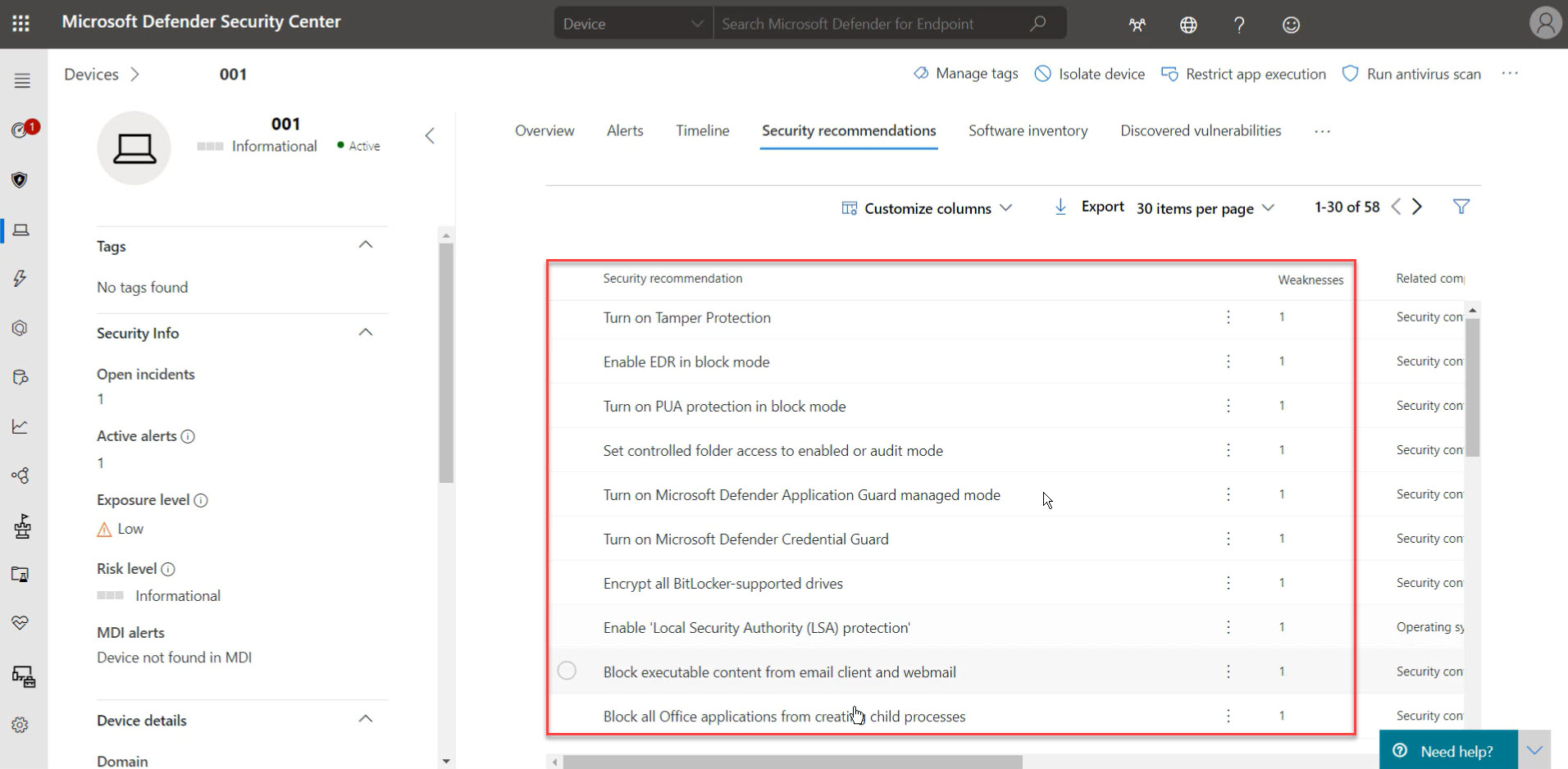
Security recommendations
Microsoft Defender also recommends activating different features in order to increase the security level of your desktops in the Security recommendations tab. In there, you can find multiple settings that you can directly enable and push into Intune when you set up the connection (covered earlier in the blog) correctly to your Intune tenant environment.
New MS Learn modules on Defender for Endpoint
Microsoft Learn is the more technical and comprehensive approach to explain products than on normal Microsoft Docs. Besides this, different use-cases are covered as well that reflect real-life customer scenarios that are easy to learn and adopt. Just recently, new modules got released that cover great insights as a follow-up to this article. I’d recommend you to take a look there too!
Practice security administration – Learn | Microsoft Docs
Need help? Visit the Defender Tech Community page
Because we all learn from each other, it’s important to connect with other people in the community around Defender. Make sure to join the Microsoft Defender for Endpoint Tech Community, as there are lots of other great follow-up articles available there as well as an opportunity to provide feedback and ask for questions directly to the product group!